For those who prefer to listen rather than read, this article is also available as a podcast on Spotify.
Contents:
Payments used to be something you plugged in at the end. Now they’re part of the core system. If your product touches money, even indirectly, you’re dealing with infrastructure that has to work under pressure, across regions, and with systems you don’t control. That’s where payment gateways come in.
On the surface, a payment gateway development looks simple. A user enters card details, clicks pay, and gets a result. Underneath, there’s a chain of requests between your system, a payment provider, card networks, and issuing banks. Some of those systems respond slowly. Some fail. Sometimes the same request is sent twice. The gateway’s job is to make sure the outcome is still correct.
That’s why building one is less about “adding payments” and more about handling uncertainty. You’re dealing with partial failures, retries, and states that change over time. If you don’t think this through early, you end up with duplicate charges, missing transactions, or logs that don’t explain anything when something breaks.
In this guide, we’ll go through how payment gateway software development actually works in practice. Not just the happy path, but the parts where things go wrong. We’ll look at the core components, how the system is usually structured, and what a realistic development process looks like. We’ll also cover the constraints that shape everything else—security, compliance, and fraud prevention—and why they’re not something you can “add later.”
If you’ve looked into crypto payment infrastructure, some of this will feel familiar. The mechanics differ, but the underlying problems—trust, consistency, and risk—are the same. And if you’re building something in this space, it’s worth paying attention to teams that already deal with these constraints on a regular basis, especially those with solid fintech development expertise.
What Is a Payment Gateway?
A payment gateway is the piece of the system that stands between your product and the banking world. It doesn’t actually move money. It makes sure the request to move money goes through correctly—and, just as important, that you understand what happened after.
In practice, it connects your app, the payment processor, card networks, and the user’s bank. None of these systems are particularly consistent, and none of them care about your UX. The gateway’s job is to smooth that out so your product doesn’t break every time something upstream behaves unpredictably.
Without that layer, you’d be dealing directly with banks and networks. That means handling raw card data, managing compliance, and building your own logic for retries, failures, and edge cases. Most teams learn pretty quickly that this is not something you want to own unless you have to.
How Payment Gateways Work
On paper, the flow looks clean. In reality, it’s a chain of systems passing a request along and hoping nothing goes wrong.
A user enters their card details and hits “pay.” That’s the only part they see.
The gateway takes that data and makes sure it’s handled securely—usually by encrypting it or passing it through a tokenized flow so your backend never touches sensitive information directly.
Next, the request goes to a payment processor. This is where things leave your system and enter the financial network. The processor routes the transaction through a card network to the issuing bank.
The bank checks a few things—whether the card is valid, whether there’s enough balance, whether the transaction looks suspicious—and sends back a response. Approved or declined.
That response makes its way back through the same chain until it reaches your system.
That’s the ideal version.
In practice, requests can time out. Responses come back late. The same transaction might be sent twice. Sometimes you get a “success” response, and then a reversal event a few seconds later. Good gateway implementations are built around this kind of behavior. Not the clean diagram—the messy reality behind it.
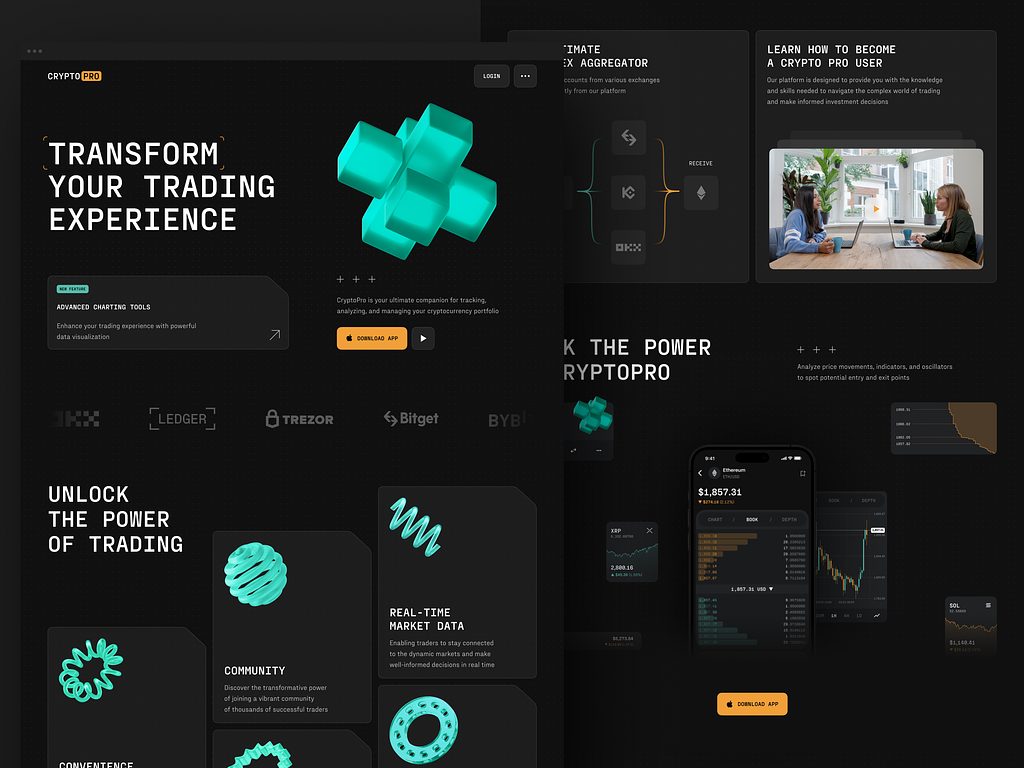
Crypto Trading Website by Shakuro
Types of Payment Gateways
The difference between gateway types mostly comes down to one question: how much of the payment flow you want to control—and what you’re willing to deal with because of that.
Hosted Payment Gateways
This is the default starting point. You don’t really build a payment flow—you hand it off.
The user clicks “pay” and gets redirected to a page owned by the provider. They enter their details there, the provider talks to the bank, and then sends the user back with a result.
It removes a lot of problems. You’re not handling sensitive data, compliance is simpler, and the whole thing is relatively hard to break.
But you’re also giving up control at the worst possible moment. The checkout experience isn’t really yours anymore. If something feels slow or off, you can’t do much about it.
Self-Hosted Payment Gateways
Here, the form stays inside your product. No redirects, no context switch for the user.
From the outside, it looks better. From the inside, it’s a different story.
You’re now closer to the data. Even if you pass everything to a provider immediately, you still need to think about how it moves through your system. Security stops being abstract. Compliance becomes something you actually have to account for.
It’s not a huge jump in complexity, but it’s noticeable.
API-Based Payment Gateways
This is where you stop relying on someone else’s flow and start building your own.
You integrate with APIs and take control over how payments behave—how they’re created, how states are tracked, how failures are handled. This usually shows up when payments are tightly tied to the product itself, something closer to digital banking infrastructure than a simple checkout.
Nothing is hidden here. If a request is duplicated, you deal with it. If a response comes late, you decide what that means. The flexibility is useful, but it comes with responsibility that’s easy to underestimate.
Key Features of a Payment Gateway Platform
Secure Payment Processing
This is the part you don’t get to compromise on.
A payment gateway is expected to handle sensitive data without leaking it, exposing it, or even holding it longer than necessary. In most cases, that means the data is encrypted as early as possible—often before it even reaches your backend—and stays that way throughout the flow.
You also don’t get to define your own rules here. Standards like PCI DSS exist for a reason, and they shape how the system is built from the ground up. Where data is stored, how it moves, who can access it—all of that is constrained before you even start thinking about product decisions.
Fraud detection sits on top of this. At first, it looks like a set of rules—block suspicious countries, flag unusual amounts, limit repeated attempts. That works until it doesn’t. As traffic grows, patterns get less obvious, and simple rules either miss problems or block legitimate users.
That’s usually where teams start looking at AI-powered fraud detection for fintech platforms. Not because it’s trendy, but because manual rules stop scaling at some point, and you need systems that can adapt to behavior instead of just reacting to it.
Crypto Trading App by Shakuro
Multi-Payment Method Support
Users don’t all pay the same way. Some use cards, some prefer Apple Pay or Google Pay, some expect bank transfers, and in certain markets, crypto is already part of the mix.
From a product perspective, supporting multiple payment methods increases conversion. From a technical perspective, it adds complexity pretty quickly.
Cards are the baseline—credit and debit, handled through the usual networks. Digital wallets sit on top of that, but come with their own flows and edge cases. Bank transfers are slower and often asynchronous, which means you’re dealing with delayed confirmations instead of immediate results.
Crypto adds another layer entirely. Different rails, different settlement logic, different expectations around finality. It’s not just “one more method”—it behaves differently enough that it needs to be treated separately, especially if you’re thinking about crypto payment integration.
The main challenge here isn’t just connecting multiple methods. It’s making them behave consistently inside your system, so the rest of your product doesn’t have to care how the payment actually happened.
Transaction Monitoring and Reporting
Once payments start flowing, you need to see what’s actually happening. Not in batches, not with delays—ideally in real time.
At a basic level, this means tracking every transaction as it moves through the system. Created, authorized, captured, failed, refunded. If something gets stuck or behaves unexpectedly, you want to catch it early, not after users start complaining.
But raw logs aren’t enough. Teams need a way to look at the system as a whole—conversion rates, failure patterns, provider performance, regional differences. That’s where reporting and dashboards come in. Not as a “nice to have,” but as a way to understand whether the system is working or quietly losing money.
This is also where things start to overlap with financial data analytics platforms. Payments generate a lot of structured data, and if you’re not using it, you’re missing signals—both for business decisions and for catching issues before they escalate.
Global Payment Support
Things get more complicated the moment you leave a single market.
Different currencies are the obvious part. You need to accept payments in whatever the user is paying with and convert it somewhere along the way. That introduces small but annoying problems—rounding, rate differences, timing between authorization and settlement.
Cross-border payments are where it starts to feel less predictable. Transactions take longer. Banks run more checks. Approval rates drop for reasons you don’t always see. The same flow that works locally can behave differently just because the card was issued in another country.
You can’t treat all of this as one uniform system. It needs to be handled with those differences in mind.
Mobile Payment Integration
Mobile is a different environment. Less space, less patience, fewer second chances.
Typing card details is something users avoid if they can. They expect built-in options like Apple Pay or Google Pay to work without friction. If that flow breaks or slows down, they usually don’t try again.
From the implementation side, this isn’t just another payment method. You’re dealing with platform rules, SDK behavior, and device-level interactions. Things don’t always behave the same way as on the web.
If mobile matters, it’s better to think about this early. Otherwise you end up adapting a web-based flow into something it wasn’t designed for. Teams with real native mobile development experience usually avoid that problem by building the flow around the platform instead of forcing it in later.
Payment Gateway Development Process
1. Product Strategy and Compliance Planning
This is where most mistakes start—treating payments like a feature instead of something with hard constraints.
Before writing anything, you need to decide what exactly you’re building. A basic checkout flow, a gateway that sits between multiple providers, or something closer to internal infrastructure. That decision affects everything that comes after. Changing it later is possible, but usually painful.
At the same time, regulation is already part of the picture.
PCI DSS defines how you handle card data. PSD2 affects authentication flows, especially in Europe. AML requirements come into play if your system starts looking less like “payments” and more like financial services.
These aren’t boxes you check at the end. They define how data moves, what you’re allowed to store, and how the user flow is structured.
This is also where scope tends to get out of control. Supporting multiple providers, regions, and payment methods from day one sounds reasonable, but it slows everything down. A narrower model is easier to stabilize, and easier to expand later.
In practice, this stage of payment processing software development is less about features and more about constraints. Strong fintech development expertise usually shows up here—in how early those constraints are identified and how much they simplify (or complicate) the system that follows.
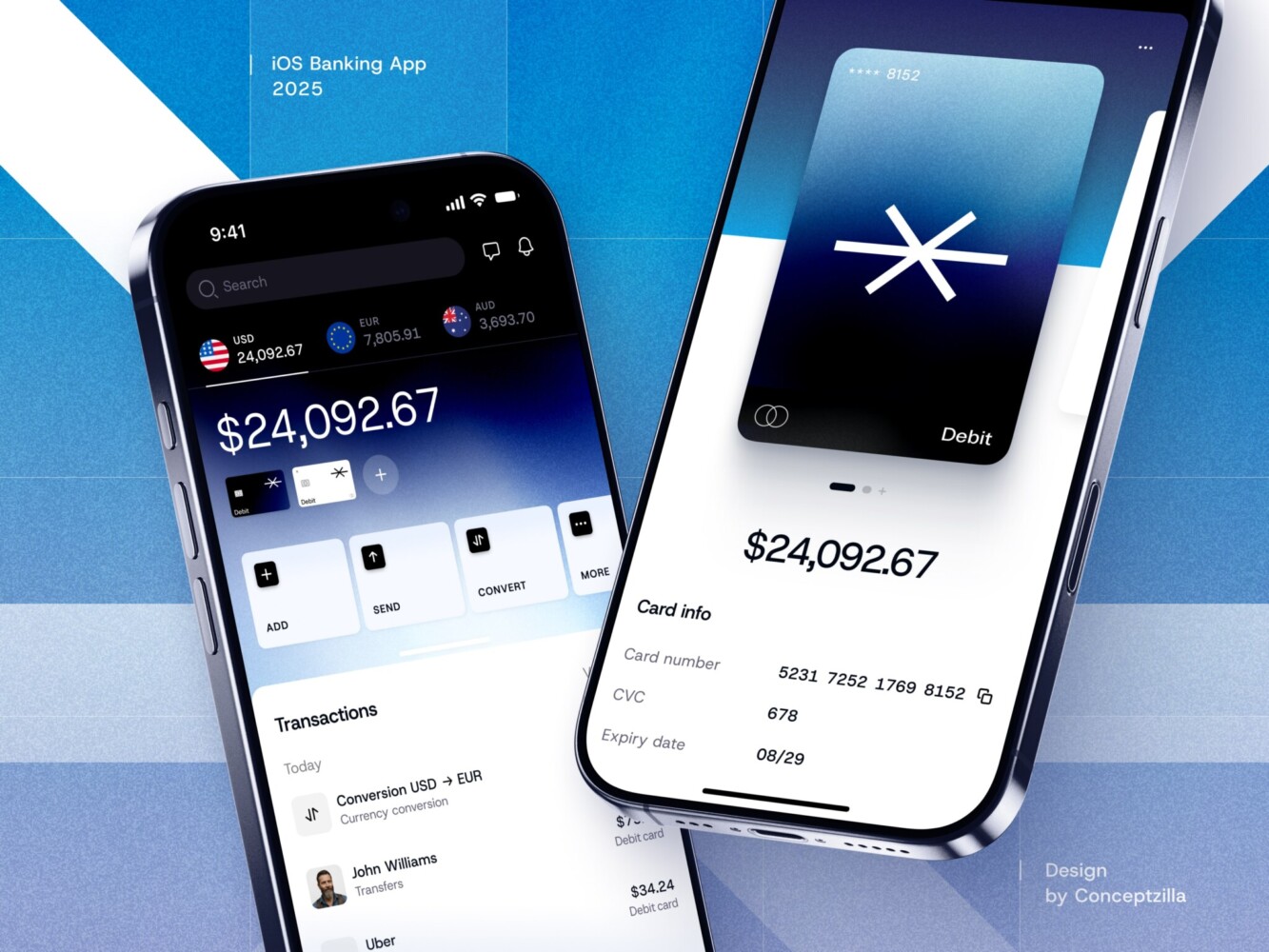
Fintech Mobile Banking App by Conceptzilla
2. UX/UI Design for Payment Systems
Payment UX is usually judged by one thing: whether the user finishes the payment or disappears.
The flow needs to feel simple, but simplicity here is deceptive. You’re asking for sensitive information, often on a small screen, sometimes under weak connection, and usually at the point where the user has the least patience. Every extra step matters.
The basic job is clear enough: make the checkout easy to follow, remove unnecessary friction, and still keep the flow secure. Users should always understand what is happening, what they need to enter, and what happens next. Confusion at this stage is expensive.
A lot of payment processing platform development problems are really interface problems. Too many fields. Unclear errors. Weak feedback after submission. A form that technically works but makes the user hesitate for two seconds longer than they should. That’s often enough to lose the payment.
This is especially noticeable in web products built with dynamic interfaces, where the payment flow has to stay fast and predictable while handling validation, state changes, and third-party logic. Good React development helps here not because it looks modern, but because it makes these interactions easier to control without turning the checkout into something fragile.
3. Choosing the Technology Stack
There’s no special stack for payments. Same tools as everywhere else. The difference is in how they behave under pressure.
On the backend, you mostly pick between stability and speed of iteration. Java and C# are common where systems are expected to run for a long time without surprises. Node.js is often used when integrations matter and things need to move faster. Python shows up in similar cases, especially with frameworks like FastAPI, where you want something simple that doesn’t slow you down early.
None of this is critical on its own. What usually causes problems is mixing too many things without a clear reason.
On the frontend, it’s less of a debate. React or Vue—both are fine. Payment flows are mostly about handling state: inputs, validation, loading, errors. If that part is messy, the user feels it immediately. Clean frontend development matters more than the framework choice.
For data, PostgreSQL is the default. Transactions need structure and consistency, and it handles that well. Redis is usually added next to it for things that don’t need to live forever—sessions, temporary states, short-lived data during the payment flow.
Infrastructure tends to follow the same pattern. Docker to keep environments consistent. Kubernetes later, if the system grows enough to need it.
None of these choices are unusual. The tricky part is how they behave together when things stop going smoothly—which they will.
Picking something like FastAPI development or C# development isn’t really about preference. It’s about what kind of problems you expect to deal with later, and how much complexity you’re willing to manage when the system is no longer small.
4. Security Architecture
This part defines the system more than anything else.
Payment data can’t just “pass through” your system in plain form. It needs to be encrypted early and stay that way for as long as possible. In many cases, the goal is to avoid handling raw card data altogether.
That’s where tokenization comes in. Instead of storing actual card details, you store a token that represents them. If something leaks, the token is useless on its own. It reduces risk, but also changes how the rest of the system interacts with payments.
Fraud prevention sits alongside this, not on top of it. At first, it’s usually basic—limits, simple rules, maybe some geo checks. Over time, that stops being enough. Patterns get less obvious, false positives increase, and you need something that can adapt to behavior rather than fixed rules.
Security here isn’t a separate layer you add later. It’s built into how the system works from the beginning. The way data is handled, stored, and passed between services all depends on it.
In some cases, parts of this logic overlap with what’s used in secure blockchain infrastructure for financial systems, where minimizing trust and limiting exposure are built into the architecture itself.
5. Integrations with Financial Systems
This is the stage of custom payment gateway development where your system stops being isolated and starts depending on everything else.
You integrate with payment processors, banks, card networks, digital wallets. Each of them has its own API, its own quirks, its own failure modes. Some respond instantly, some don’t. Some return clear errors, others don’t bother.
There’s no single pattern that works for all of them. You end up building adapters, normalizing responses, retrying requests, and keeping track of states that don’t always line up.
The complexity isn’t in connecting to one system. It’s in making all of them behave consistently inside yours. Especially when they don’t behave consistently on their own.
This layer often overlaps with things you’d expect from core banking systems and financial infrastructure—not because you’re building a bank, but because you’re dealing with the same kind of coordination problems.
And since most of this logic sits on the server side, solid web development services usually show up here in how integrations are structured and maintained over time.
6. Testing and Compliance Validation
Payments don’t fail in obvious ways. That’s what makes testing harder.
You’re not just checking if a request succeeds. You’re checking what happens when it doesn’t. Timeouts, duplicate requests, delayed responses, partial failures—those are the cases that matter.
Transaction flows need to be tested end-to-end, including scenarios that are hard to reproduce. What happens if the bank responds late? What if the same payment is submitted twice? What if the confirmation never arrives?
Security testing runs in parallel. Audits, penetration testing, verification of how data is handled. Not because it’s good practice, but because it’s required.
Compliance validation is the final layer. You’re checking that the system matches the rules you designed around earlier. If it doesn’t, fixing it later is much harder.
7. Deployment and Maintenance
Launching the system isn’t the end of the work. It’s where most of the real issues start to show up.
You need visibility into what’s happening—logs, metrics, alerts. If transactions start failing or slowing down, you need to see it before users do.
Fraud monitoring becomes an ongoing process. Patterns change, behavior shifts, and the system has to adapt. What worked at launch won’t be enough later.
Updates are continuous. New payment methods, changing regulations, provider updates. The system doesn’t stay still, so neither does the code.
Ongoing support services usually cover this part—keeping the system stable, responding to issues, and making sure it keeps working as conditions change.
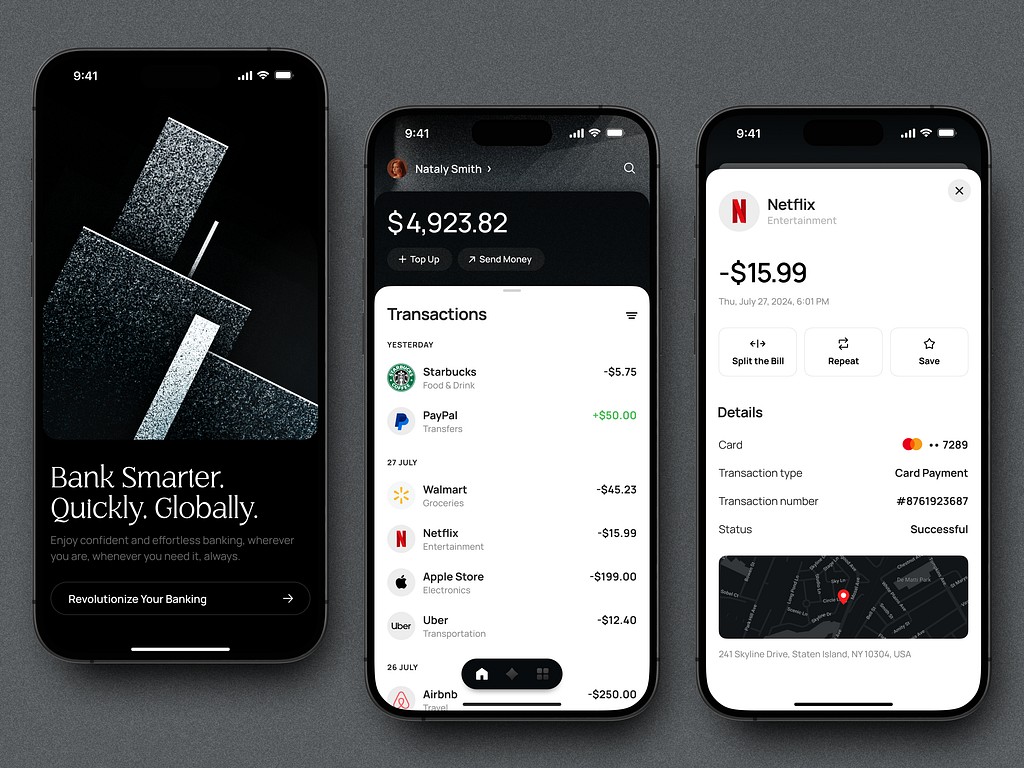
Fintech Mobile App UI Design by Shakuro
Cost of Payment Gateway Software Development
There’s no fixed price for a payment gateway. It depends on how far you go.
Some teams start with a simple setup—one provider, one region, basic flow. Others build something that connects multiple systems and has to hold up under real load. The gap between those two is big.
A few things drive most of the cost:
– compliance requirements (PCI DSS, PSD2, AML)
– integrations with banks, processors, payment providers
– fraud detection and monitoring
– scalability and infrastructure
Compliance is usually the first constraint. Once you deal with card data or operate in multiple regions, the system has to follow certain rules. That affects how data moves, what you can store, and how the flow is structured.
Integrations add up quickly. One provider is manageable. Several providers, different regions, fallback logic—it gets harder to keep things consistent.
Fraud detection starts simple and becomes more complex over time. At low volume, basic rules are enough. Later, they’re not.
Scalability is where problems tend to show up late. The system works fine until it doesn’t. Requests start timing out, transactions duplicate, states don’t match. Fixing that after launch is usually more expensive than planning for it early.
In terms of scope, there are two common scenarios.
An MVP gateway is narrow. One provider, limited functionality, controlled environment. The goal is to get payments working without solving everything at once.
An enterprise platform is at a different level. Multiple integrations, global coverage, higher load, stricter requirements. At that point, you’re dealing with infrastructure, not just a feature.
That’s why costs vary so much. It’s less about “how much does it take to build” and more about what exactly you’re trying to build. The difference becomes noticeable when you move from a simple setup to full payment processing software development, where a payment gateway development company is usually brought in because the system stops being simple pretty quickly.
Common Challenges in Payment Gateway Development
Most of the real problems show up after launch.
At first, everything works in a controlled setup. Then traffic grows, edge cases appear, and the system starts behaving differently.
The usual pressure points look like this:
– compliance with financial regulations
– payment security and fraud
– growing transaction volume
– global payments
Compliance is not static. Requirements change, especially across regions. Something that’s fine in one market can become an issue in another. You don’t notice it until you expand.
Security is never “done.” You protect the data, set up basic rules, and then fraud patterns change. What worked before stops working, or starts blocking real users. You keep adjusting.
Volume changes behavior. Requests get delayed, repeated, or arrive out of order. Things that almost never happened in testing become normal. If the system isn’t built for that, it starts to break in small ways.
Global payments add more inconsistency. Different currencies, different banks, different approval logic. The same transaction flow can behave differently depending on where it comes from.
None of this is isolated. Problems overlap, and it’s not always clear where the issue actually is. That’s why systems often rely on financial transaction analytics systems—not for reporting, but to see patterns you wouldn’t catch otherwise.
Our Experience in Fintech Platform Development
Most payment systems don’t live on their own. They’re part of something larger—analytics tools, SaaS platforms, internal financial products. Payments are just one piece in a system that has to stay consistent under load.
That’s the kind of work this usually turns into. Not isolated features, but connected systems.
Across projects, the pattern repeats: payment flows, financial data, user interaction, all tied together. This shows up across fintech development expertise and broader SaaS product development, where the system has to keep working even when different parts move at different speeds.
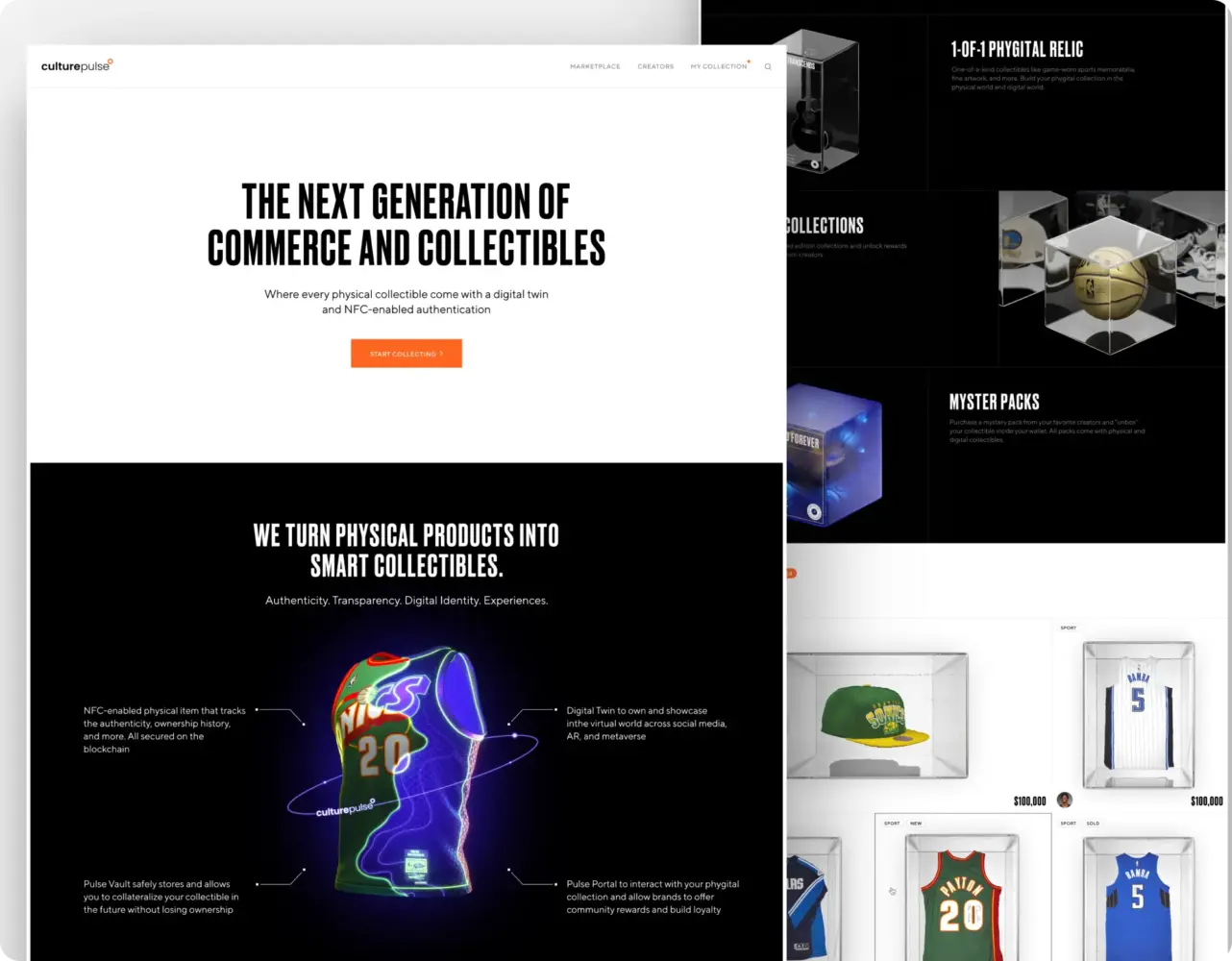
Case: Culture Pulse—Phygital Collectibles Marketplace
Culture Pulse combined physical collectibles with digital ownership.
Web3-Infused Technology and Collectibles Brand by Shakuro
Athletes and creators could release limited drops—shirts, sneakers, memorabilia—paired with digital copies stored on blockchain. Each physical item included an NFC chip. The digital version worked as proof that the item was real.
The challenge wasn’t just technical. It was clarity.
Most users weren’t familiar with how physical and digital ownership connect. The platform had to explain that without turning the interface into documentation.
A lot of effort went into the presentation. Every collectible was different, but the platform still needed to feel consistent. Navigation had to stay simple. The buying flow had to feel familiar, even though the model behind it was new.
The solution focused on structure and visuals. Clear navigation, marketplace-style layout, and explanatory graphics helped users understand what they were buying and how ownership worked.
Systems like this sit close to secure blockchain infrastructure for financial systems, where transactions and ownership history have to stay verifiable over time.
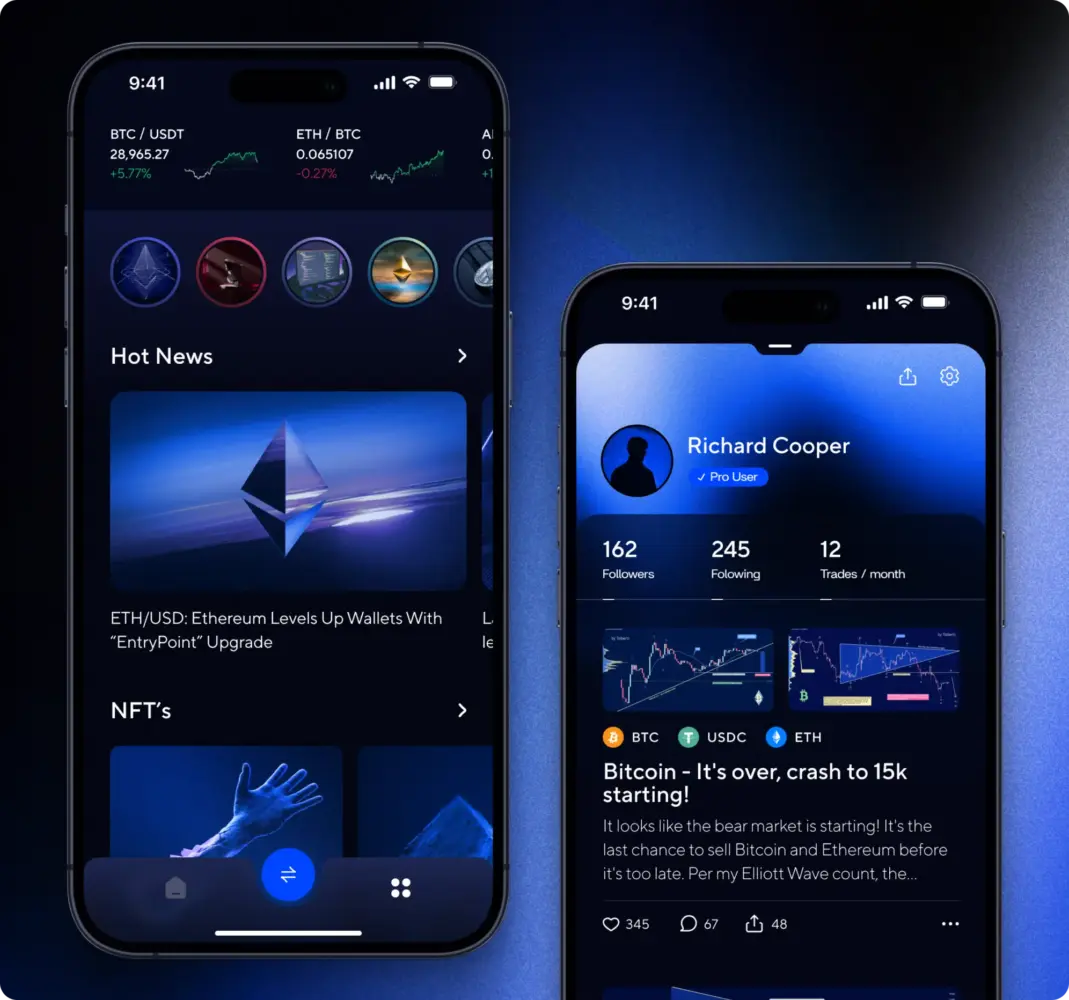
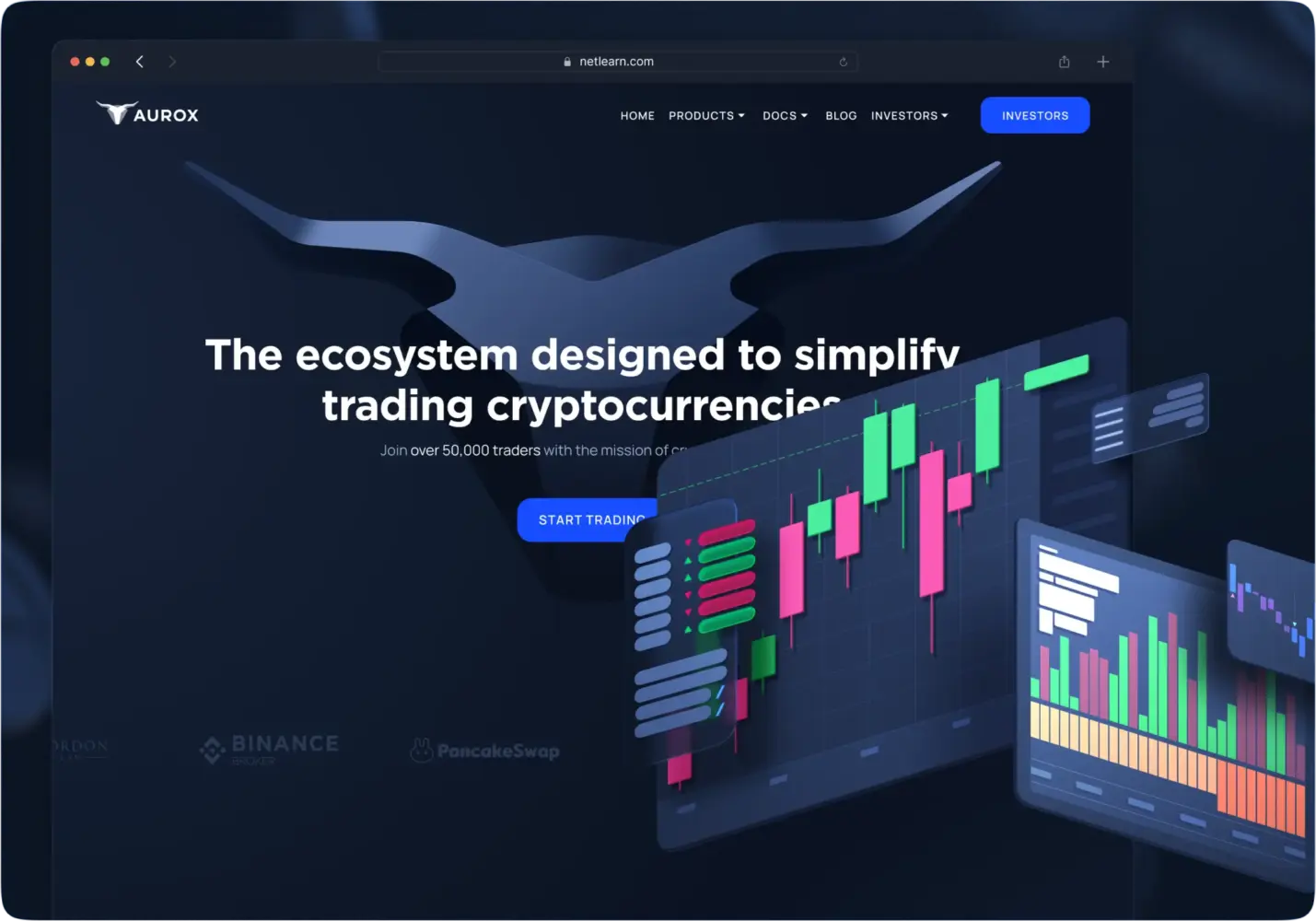
Case: Aurox—Crypto Trading Ecosystem
Aurox was not one product. It was a group of connected tools.
Premier Crypto Trading Ecosystem Design by Shakuro
Trading terminal, wallet, token ecosystem, DeFi components. Each part had its own role, but users had to experience them as one system.
The first problem was consistency. The products existed, but the experience across them wasn’t unified.
That becomes risky in crypto. Users rely on visual clarity more than they admit. If the interface feels chaotic, trust drops quickly.
The work focused on building a shared visual system that could stretch across different tools. Trading interfaces, dashboards, wallet screens—all needed to feel related without becoming identical.
Performance was another concern. Trading tools behave differently from standard web apps. Real-time updates, large data sets, fast interaction. Delays are noticeable immediately.
So the focus stayed on structure—navigation, layout, and visual hierarchy that could handle heavy workflows without slowing people down.
Such projects usually overlap with financial transaction analytics systems, where large volumes of data move constantly and need to stay readable.
Why Work with a Payment Gateway Development Company
You can build payments yourself. At the beginning, it often works fine.
Then things get less predictable. Requests fail in ways you didn’t expect. Providers behave differently. Compliance questions come up later than they should have.
That’s usually the point where it becomes clear this isn’t just another feature.
Working with a payment gateway development company who’s done this before mostly changes how early problems are handled. Instead of reacting to issues later, a lot of them are accounted for upfront.
Compliance is one of those. Requirements like PCI DSS or PSD2 aren’t something you “add.” They affect how the system is structured from the start—what data you handle, how it moves, what you’re allowed to store.
The same with architecture. Payments don’t behave perfectly. Requests get delayed, repeated, or fail halfway through. If the system isn’t built for that, you end up patching it later.
Security follows the same pattern. It’s not a separate layer. It’s part of how everything works.
In simple terms, the benefits of collaborating with payment gateway developers look like this:
– fewer surprises with compliance
– a system that holds up when traffic grows
– transaction flows that don’t expose more than they should
This kind of approach usually comes from teams with real fintech development expertise, where these problems show up often enough that they’re planned for, not discovered later.
Final Thoughts
Building a payment gateway follows a familiar path. You start with an idea, define the architecture, build the system, and eventually launch it.
What matters is what happens in between those steps.
Payments don’t tolerate weak spots. If something breaks, it’s visible immediately—failed transactions, missing confirmations, inconsistent states. Most of the work is making sure the system behaves predictably even when everything around it doesn’t.
The core things don’t change:
– security — how data is handled and protected
– reliability — whether the system behaves consistently under load
– compliance — whether it operates within the required rules
– scalability — whether it holds up as volume grows
Miss one of these, and problems show up sooner or later.
If you’re building a payment system, it’s worth treating it as infrastructure from the start. That usually means working with people who’ve already dealt with these constraints in real projects.
Shakuro works with fintech products where payments are part of a larger system, not an isolated feature. If you’re planning to build or scale payment infrastructure, having that kind of context early tends to save time later.
