For those who prefer to listen rather than read, this article is also available as a podcast on Spotify.
Contents:
Cryptocurrency products have grown far beyond simple trading tools. Today digital assets are used in financial platforms, games, creator economies, and decentralized applications. As more services start working with blockchain networks, one practical question appears almost immediately: where and how will users store their assets?
Unlike traditional finance, blockchain systems do not rely on centralized accounts. There is no bank that holds your balance and restores access if something goes wrong. Control over funds comes down to one thing—the private key. Whoever holds that key can move the assets tied to it. If it is lost or compromised, the assets are gone.
This is exactly the problem crypto wallets solve.
A wallet is the piece of software that manages private keys and allows a user to interact with a blockchain. Through a wallet, people can send tokens, receive payments, check balances, or connect to decentralized applications. In many cases the wallet becomes the main interface between a user and the blockchain itself.
For companies building blockchain products, cryptocurrency wallet development is more than just an additional feature. Exchanges, DeFi platforms, NFT marketplaces, and tokenized services all depend on wallet infrastructure. Some projects use existing wallets, but most teams end up making their own. A personalized wallet makes it easy to support certain networks, regulate the security architecture, and design the user experience around the product.
This approach is common in projects that operate inside a broader Web3 development ecosystem, where wallets need to interact with smart contracts, tokens, and decentralized applications without friction.
In this guide we’ll look at how crypto wallets are actually built and what decisions shape their architecture. We’ll cover:
- the different kinds of crypto wallets and how they operate
- how the infrastructure of a wallet is built up
- ways to keep private keys safe
- common steps for making a wallet
Wallets rarely exist in isolation. They usually operate alongside other parts of a blockchain platform—trading engines, liquidity services, or market infrastructure. Understanding that context helps explain many design choices behind wallet systems. If you want to see how these components connect, it’s useful to look at how modern platforms design their crypto exchange infrastructure.
What Is a Crypto Wallet?
A crypto wallet sits between the user and the blockchain. It manages the keys tied to an address and uses them to sign transactions.
It doesn’t store assets. Coins and tokens live on the chain. The wallet deals with the private key—the one thing that defines control over an address. If you have it, you can move funds. If you don’t, you can’t.
When a transaction is sent, the wallet builds it, signs it locally, and pushes it to the network. After that, validation happens on the node side. What the user sees is a simple action—send, receive, check balance—but the wallet is doing the only part that actually requires trust: handling the key.
In most products, that same mechanism is reused for authentication. Instead of accounts, users connect a wallet and sign a message. That signature becomes the identity layer across many blockchain applications and infrastructure, whether it’s a DeFi protocol or a marketplace.
Types of Crypto Wallets
Wallets are usually described by two variables: who holds the key and where it lives.
Custodial Wallets
In a custodial model, keys are held by the platform. The user operates through an account, while the service manages custody and signing on its side.
This is how exchanges work. It lowers the entry barrier, but control sits with the platform.
Non-Custodial Wallets
Non-custodial wallets keep keys on the user’s side. They’re generated locally and aren’t handed off to a backend.
There’s no intermediary here. There’s also no recovery mechanism beyond the recovery phrase.
Hot Wallets
Hot wallets are always online and communicate with the network directly. This group includes mobile apps and wallets that work in web browsers.
They’re used for regular activity—transfers, swaps, contract interactions.
Cold Wallets
Cold wallets keep keys offline. Hardware devices are the typical example.
They’re slower to use, but the attack surface is much smaller, which is why they’re used for storage rather than day-to-day operations.

Crypto Finance App UI/UX Design by Shakuro
Key Features of a Secure Crypto Wallet
Security in a wallet is mostly about key handling. Everything else is secondary. If the key leaks, nothing else helps.
The design usually focuses on three moments: when the key is created, where it lives, and how it’s used for signing. Each of those points is a potential failure surface.
Private Key Management
In non-custodial wallets, keys are generated on the client and stay there. They aren’t sent to a backend or stored remotely. That’s the baseline.
On the device, keys are kept encrypted. Access is gated by something the user controls—password, PIN, biometrics. The implementation details vary, but the idea is simple: getting access to storage shouldn’t be enough to use the key.
Seed phrases are used for recovery. They’re just another representation of the same key material, but in a format that can be written down and restored elsewhere. Convenient, but also fragile—anyone with the phrase has full access.
In custodial systems, keys sit on the platform side. Here the problem shifts from device security to infrastructure. Access is restricted, environments are isolated, and key operations are often pushed into hardware modules. Hardware security modules are used to generate and store keys in a controlled environment and to handle signing without exposing raw key material.
Different models, same constraint: the key should never appear in plain form outside a controlled context, and access to it should always require an explicit action.
Multi-Currency Support
Supporting more than one chain sounds simple on paper. In practice, it shapes most of the wallet architecture.
Different blockchains don’t behave the same way. Bitcoin uses a UTXO model. Ethereum is account-based. Transaction formats, fee logic, signing rules—all of that changes from one network to another. A wallet that works across chains has to abstract those differences without breaking expected behavior.
At a minimum, that means separate handling for each network: key derivation paths, transaction builders, fee estimation, and node interaction. You don’t really get a “universal wallet”—you get a layer that coordinates multiple implementations under one interface.
Ethereum and Bitcoin are usually the starting point. From there, teams add EVM-compatible chains, then others depending on the product—Solana, Tron, or whatever the use case requires. Each addition increases surface area, especially around signing and validation.
Token support adds another layer. On Ethereum alone, ERC-20, ERC-721, ERC-1155—different standards, different interaction patterns. The wallet has to recognize them, display them correctly, and handle contract calls without exposing raw complexity to the user.
The hard part isn’t listing more assets. It’s keeping behavior consistent while the underlying systems are not.
Transaction Management
Sending a transaction isn’t just filling in an address and amount. The wallet has to assemble it properly, sign it, and get it accepted by the network. That means dealing with whatever model the chain uses—UTXOs on Bitcoin, nonces and gas on Ethereum—and making sure the transaction won’t just sit in the mempool.
Receiving is simpler in mechanics, but not in handling. The wallet generates addresses and watches for incoming transfers, then decides when to surface them as “received.” That usually depends on confirmations, not just detection.
After broadcast, the wallet tracks the transaction state. Pending, included, confirmed—different stages, different signals from the network. Some wallets poll nodes, others subscribe to updates, but either way they maintain their own view of what’s happening.
Where it gets tricky is consistency. Transactions can be delayed, repriced, or replaced. Fees spike, blocks fill up, nodes fall out of sync. The wallet has to deal with all of that quietly and still present a clear state to the user.
This becomes stricter in payment scenarios. You can’t treat a transaction as final just because it appeared in a block. Confirmation depth matters, edge cases matter. That’s why wallets used in crypto payment infrastructure tend to treat transaction state as part of the system logic, not just a UI detail.
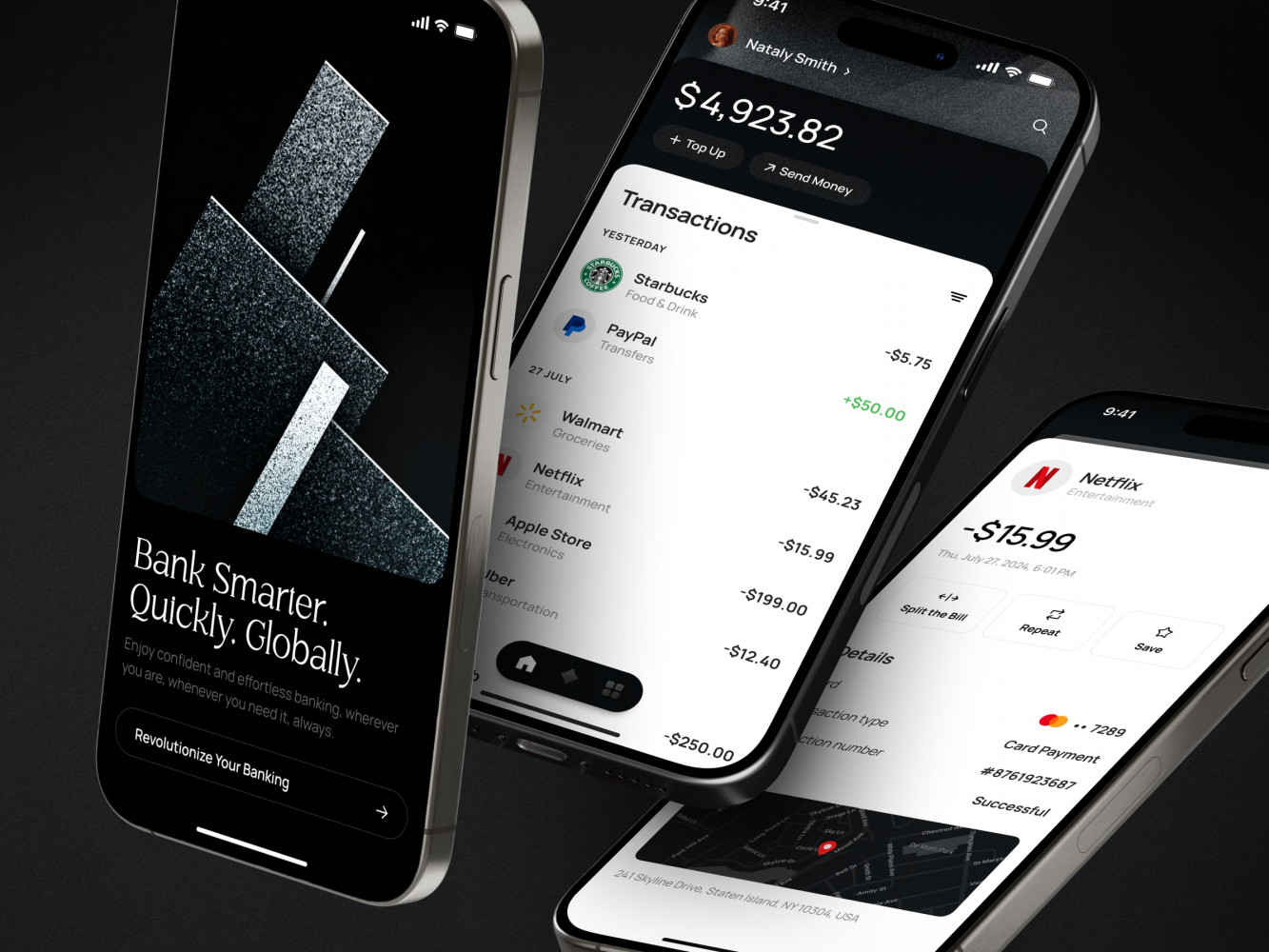
Finance Management Mobile App Design by Shakuro
Security and Authentication
Authentication is where the user actually meets the security model. If this part feels off, everything else does too.
Most wallets add a second factor on top of basic access—codes, apps, sometimes hardware tokens. It’s not bulletproof, but it raises the cost of unauthorized access, especially in custodial setups.
On mobile, biometrics are usually the default. Fingerprint, Face ID—quick to use, tied to the device, and good enough for day-to-day access. Underneath, it still maps to a local unlock mechanism that gates access to the key.
Sensitive data stays encrypted at rest. That includes keys, but also anything tied to them—backups, cached state, session data. Decryption only happens when needed, and ideally not for longer than a single operation.
Fraud detection sits a bit outside the wallet itself. It’s less about blocking access and more about spotting patterns—unusual transactions, repeated behavior, anomalies in how the wallet is used. In larger systems, this connects to AI-based fraud detection systems, where activity is analyzed across accounts and time, not just within a single session.
Cross-Platform Accessibility
Wallets rarely live in a single environment. Users expect access from wherever they are—desktop, mobile, browser. That shapes how the product is split across platforms.
Web wallets are usually the lightest entry point. No installation, quick access, easy to onboard. At the same time, they depend on the browser environment, which limits how keys are stored and how securely they can be isolated.
Mobile wallets are where most products settle long-term. They have better access to secure storage on the device and can rely on system-level features like biometrics. They also make more sense for day-to-day use—payments, quick transfers, notifications. That’s why teams investing in wallets often prioritize native mobile development early on instead of treating mobile as a secondary layer.
Browser extensions sit somewhere in between. They’re tightly integrated with web apps and are the default way to interact with many decentralized services. The extension acts as a bridge—injecting the wallet into the browser so dApps can request signatures and read account data.
The challenge isn’t building each version separately. It’s keeping behavior consistent across them while dealing with very different environments underneath.
Crypto Wallet Development Process
1. Product Strategy and Wallet Type Selection
This is where most of the real decisions are made. Everything that follows depends on it.
The first choice is custody. Custodial and non-custodial wallets are different products, not just different implementations. Custodial means the platform holds the keys and takes responsibility for security, recovery, and compliance. Non-custodial means the user holds the keys and the system is built around that constraint. Switching between the two later is expensive, so this is usually fixed early.
Next is asset support. It’s not just a list of coins. Each chain brings its own rules—transaction model, fee mechanics, signing logic. Supporting Bitcoin and Ethereum already means dealing with two very different systems. Adding more networks scales complexity quickly, especially if the product needs to handle tokens, not just native assets.
The user profile comes next. A wallet for traders behaves differently from a wallet for long-term storage or payments. Speed and integrations are important to traders. Users who are focused on storage are concerned about recovery and isolation. Payment flows have their own rules on confirmations and trustworthiness. This is where the product starts to come together.
At this stage, teams usually define how the wallet fits into a larger system. In many cases it’s not a standalone product but part of a broader platform—exchange, payment service, or DeFi application. That’s where considerations around crypto trading ecosystems start to influence the architecture early on.
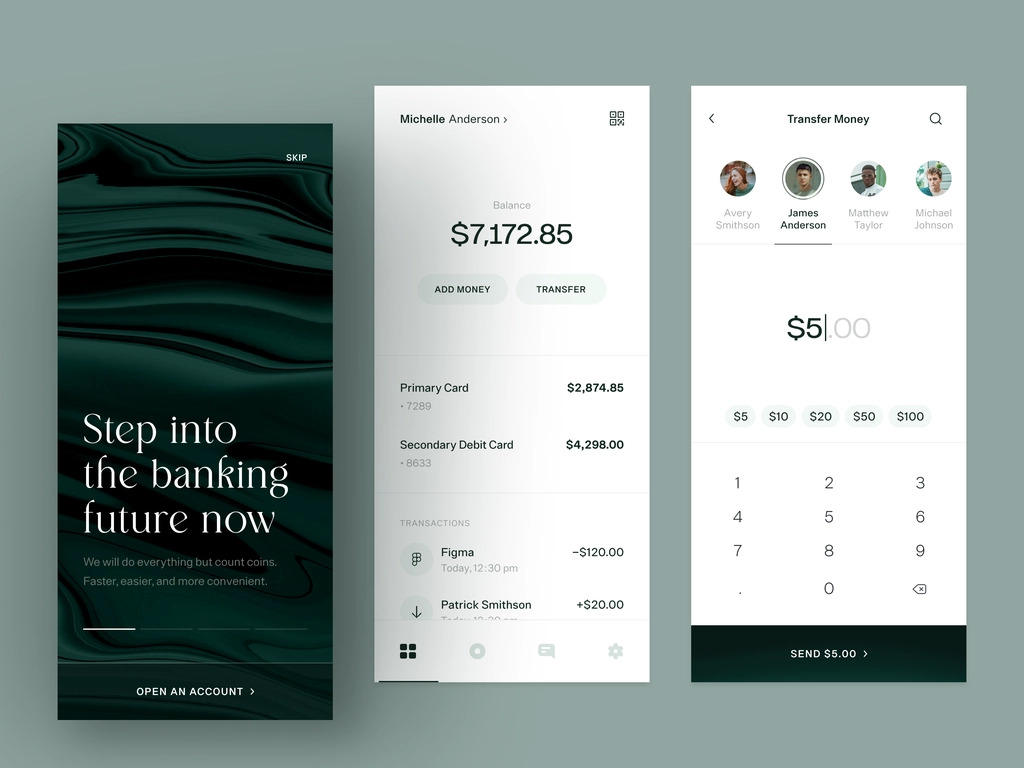
Finance Management Mobile App by Shakuro
2. UX/UI Design for Wallet Applications
Wallet UX is where a lot of products fail. Not because the features are missing, but because the flows don’t match how people actually use crypto.
The interface has to stay simple, even though the underlying logic isn’t. Sending, receiving, switching networks, checking balances—all of that should be obvious without explanation. If a user has to think about what to press next, something is off.
Sending is the most sensitive flow. Address input, amount, fees—too many points where mistakes happen. Good wallets reduce that surface: clear validation, readable fees, predictable steps. Same with receiving—generating an address should be instant, and the result should be easy to copy, share, or scan.
A lot of complexity sits just below the surface. Token standards, network switching, transaction states—the UI has to deal with it without exposing unnecessary detail. The goal isn’t to hide everything, but to show only what matters at the moment.
On the implementation side, most web wallets end up as state-heavy interfaces—balances, pending transactions, network status, token lists, all changing at once. Managing that without things breaking or lagging usually means relying on a predictable frontend layer, which is why teams often lean on React development for this kind of work.
3. Choosing the Technology Stack
The stack usually reflects earlier choices—custody, supported chains, expected load.
On the backend, it’s mostly about keeping things predictable under load. Node.js is often used for API layers and anything that needs to get updates in real time. Python, frequently with FastAPI, is utilized in services where teams wish to build and keep things simple. Go tends to be used where concurrency matters: transaction pipelines, workers, queue processing. In most cases, it’s not one language across the board but a mix, depending on what each service needs to do.
On the frontend, it usually comes down to React or Vue. Not for stylistic reasons—wallet interfaces tend to carry a lot of moving state at once. Balances update, transactions change status, networks switch, tokens come and go. Without a clear structure, it gets messy fast. That’s why frontend development here usually leans toward frameworks that don’t fall apart when everything updates at the same time.
Blockchain integration doesn’t unify well. Each network has its own rules. Ethereum is built around RPC calls and account-based logic. Bitcoin works with UTXOs and different transaction assemblies. Solana has a completely different execution model. Supporting several chains means maintaining separate integrations, even if they’re hidden behind one interface.
On the infrastructure side, Docker is the default for packaging services. Kubernetes comes in once there are enough moving parts to justify orchestration. Not always on day one, but usually sooner than expected.
If Python is part of the stack, FastAPI often ends up in the mix—not because it’s trendy, but because it’s fast to work with and doesn’t get in the way. That’s typically where FastAPI development fits into wallet backends.
4. Wallet Security Architecture
Security here isn’t a feature—it’s how the wallet is put together. Most of it comes down to one question: where the key can exist, and for how long.
Encryption is the baseline. Keys are stored encrypted and only decrypted at the moment of signing. Even then, they shouldn’t hang around in memory longer than needed. The rest depends on the environment—secure enclaves on mobile, OS-level storage, or isolated services on the backend.
Storage splits depending on the model. In non-custodial wallets, everything stays on the device. The risk is local—extraction, malware, compromised OS. In custodial systems, keys move server-side, and the focus shifts to access control and isolation. That’s where hardware-backed storage comes in—keys don’t leave that boundary, and signing happens inside it.
Most real attacks don’t try to break encryption. They go through the user. Phishing pages, fake prompts, clipboard swaps. The wallet can’t fully control that, but it can make certain things harder—clear transaction previews, explicit signing steps, warnings when something looks off.
In larger systems, wallet-level protection is usually not enough on its own. Suspicious activity is tracked outside the wallet—patterns, anomalies, unusual flows. That’s where it starts to overlap with financial monitoring and analytics systems, not as a feature, but as another layer around it.
5. Development and Blockchain Integrations
This is where the wallet actually connects to the chain. Everything before that is preparation.
At the lowest level, the wallet needs access to nodes. Sometimes that’s a direct connection, sometimes through providers. Either way, it’s how the wallet reads state and pushes transactions out. Reliability matters here—if the node lags or drops, the wallet feels broken.
Address generation follows a deterministic pattern. Given the same seed, the wallet derives addresses in a fixed sequence, so they can be reproduced when needed rather than stored one by one. This is how wallets keep address management predictable across devices.
Signing stays local in non-custodial setups. The transaction is created, signed with the private key, and then submitted to the network. Signing happens in the backend of custodial systems, usually in separate services. Different flow, same need: the key doesn’t leak.
Once the transaction is signed, it’s sent out to the network through a node or provider. From that point on, the wallet just follows what happens to it—whether it gets picked up, included in a block, and how many confirmations it collects.
Most wallets don’t stop at basic transfers. They also connect to smart contracts—swaps, staking, liquidity operations. That’s where integration starts to overlap with broader DeFi ecosystem integrations, since the wallet becomes the entry point into those flows.
If there’s a web layer involved—dashboards, browser access, embedded flows—it usually sits on top of standard APIs that handle node communication and transaction logic. That’s where web development services come into play, connecting the wallet logic to a usable interface.
6. Testing and Security Audits
This is where small inconsistencies tend to surface.
Wallets deal with keys and transactions you can’t undo, so it’s less about “does it work” and more about how it behaves when something goes off—wrong fee estimates, slow nodes, partial data.
Security audits start with key handling. Where the key lives, when it’s accessed, what can reach it. In custodial systems, that extends into the infrastructure—service boundaries, internal permissions, signing flows.
Blockchain interactions are harder to simulate cleanly. Transactions don’t always behave the same way—they can sit unconfirmed, get replaced, or arrive out of order. Nodes can disagree for a while. The wallet has to keep its own state aligned with that, without jumping to the wrong conclusions.
Penetration testing focuses on exposed parts of the system. APIs, integrations, anything that accepts input from the outside. In wallets, that often comes down to whether transaction data can be altered before signing or whether signing can be triggered in unexpected ways.
Most problems show up at those edges, not in the main flow.
7. Deployment and Maintenance
Launching the wallet is just the point where it starts running in real conditions.
The initial release usually exposes things that didn’t show up earlier—edge cases, network inconsistencies, user behavior you didn’t plan for. That’s expected. Wallets don’t operate in isolation, and the environment is not stable.
Infrastructure needs to be watched continuously. Node availability, response times, transaction delays—if something drifts, it shows up in the wallet almost immediately.
Updates are not occasional. Networks change, fee models shift, new token standards appear. Security fixes come up regularly as well. The wallet has to keep up without breaking existing flows or exposing new risks.
Maintenance also includes user-facing support. Lost access, stuck transactions, incorrect balances—these cases come up all the time, especially in custodial systems. Support services become part of the product, not just an add-on.

Dashboard Design for Stock Trading Platform by Shakuro
Cost of Crypto Wallet Development
Costs don’t come from a single source here. They build up from a set of decisions made early—and most of them are structural, not cosmetic.
The first one is custody. A custodial wallet shifts complexity into the backend: infrastructure, security layers, access control, compliance. A non-custodial wallet moves that complexity to the client side—key storage, recovery flows, device-level security. Both can be expensive, just in different places.
The number of supported networks adds up quickly. Each blockchain is a separate integration with its own rules—transaction model, signing logic, fee handling. Supporting Bitcoin and Ethereum already means maintaining two distinct paths. Adding more chains increases both cryptocurrency wallet development and maintenance effort.
Secure crypto wallet development is another major factor. Basic encryption is not enough in most cases. Once you start adding secure storage, isolation layers, signing controls, and audit requirements, the scope grows. In custodial systems, infrastructure security alone can take a significant part of the budget.
Integrations tend to look simple until you start wiring them up. A direct node connection behaves differently from a hosted provider. Smart contract calls introduce their own edge cases. Every additional layer needs to be tested against real network behavior and then maintained over time.
Most teams end up choosing between two directions.
One is a stripped-down wallet. A couple of networks, basic transfers, minimal interface—enough to see if the product makes sense without committing to the full build.
The other is a full product from the start. Multiple chains, token handling, contract interactions, tighter security, support across platforms. At that point, the wallet is just one part of a larger system.
That’s usually what people mean when they talk about a crypto wallet development company—not just the app, but everything around it. The same goes for blockchain wallet development in general. The visible part is small compared to the infrastructure and integrations behind it.
Common Challenges in Crypto Wallet Development
Some problems show up in every wallet project, no matter the stack or use case. They’re not tied to a specific technology—they come from how blockchains work.
Key management is the obvious one. It’s easy to say “keep the key safe,” harder to define what that means in practice. On mobile, you rely on the OS. In browsers, you don’t get the same guarantees. In custodial systems, the problem shifts to infrastructure and access control. Different setups, same pressure point.
Multi-chain support is another constant source of friction. Each network has its own rules, and those differences don’t disappear behind a shared interface. You end up maintaining separate logic for signing, fees, and transaction handling, even if the UI looks unified.
User-side attacks are harder to deal with than technical ones. Phishing, fake interfaces, clipboard swaps—none of that requires breaking encryption. The wallet can warn, validate, or slow the flow down, but it can’t fully control the environment it runs in.
Then there’s the network itself. Transactions don’t always behave predictably. Fees change, blocks get delayed, nodes fall out of sync. From the user’s perspective, the wallet is responsible for all of it, even though most of it happens outside the app.
These challenges become more visible in systems that interact with trading logic or automation. In those cases, the wallet is just one part of a larger flow, often tied into automated trading infrastructure, where timing, state consistency, and transaction handling have to line up across multiple components.
Our Experience in Web3 and Fintech Development
We’ve worked on blockchain and finance systems where the wallet is only one part of a bigger system. Most of the time, it sits next to trading logic, analytics, or payment processes, so people don’t usually think about the wallet by itself.
That usually means dealing with infrastructure early—node integrations, transaction pipelines, data consistency. The same applies to digital finance platforms: once real assets are involved, the requirements shift toward reliability, not just features. Scalable SaaS architecture comes into play for products that need to handle growth without rewriting core parts. Security follows from that—not as a separate layer, but as part of how the system is structured.
This kind of work tends to overlap across domains. Projects that start as Web3 products often end up touching fintech concerns, and vice versa. That’s reflected in how teams approach Web3 and fintech as connected areas rather than separate tracks.
Two projects illustrate how this plays out in practice.
ATX was built as a mobile product combining a wallet with a simplified investment flow. The idea wasn’t to compete with advanced trading tools, but to remove the entry barrier. The interface had to stay clear while still exposing real functionality—asset tracking, buying and selling, basic portfolio logic. A lot of effort went into making the app feel approachable without turning it into a toy product. The result is a wallet experience that looks familiar to experienced users but doesn’t overwhelm newcomers.

Crypto Trading App and Wallet Experience by Shakuro
Aurox is a different scale. It’s not a single product but an ecosystem—trading terminal, wallet, DeFi protocol, token. The challenge there was consistency. Different tools, different levels of complexity, but they all had to feel like part of the same system. That included the wallet layer as well, which had to align with trading flows and protocol logic rather than exist on its own.
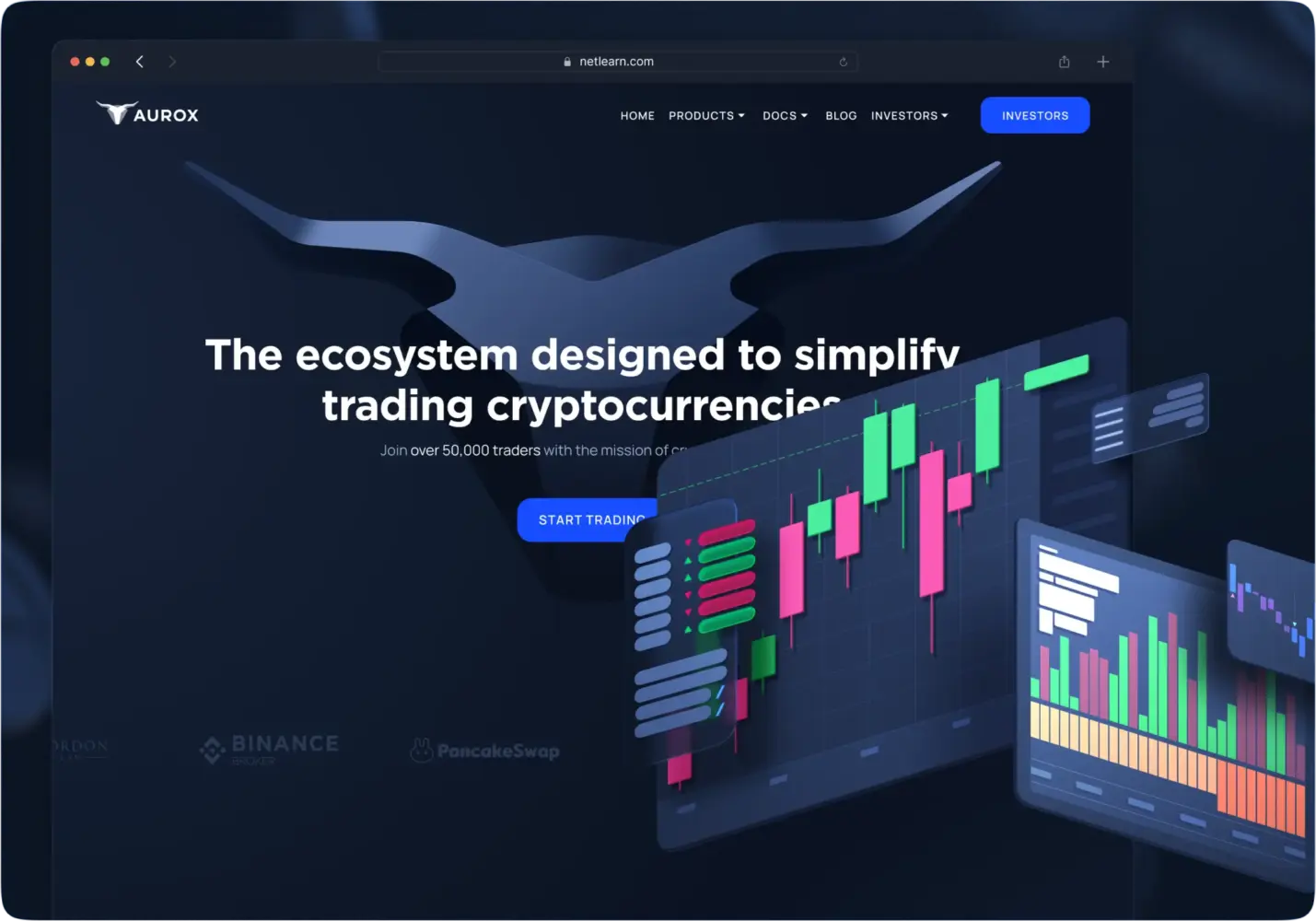
Premier Crypto Trading Ecosystem Design by Shakuro
In both cases, the wallet is not treated as an isolated feature. It is part of an overall framework that includes trading, analytics, or investment flows.
Why Work with a Crypto Wallet Development Company
Wallets look simple from the outside. In practice, they sit on top of several layers—key management, blockchain integration, infrastructure, UI. Building all of that from scratch without prior experience usually slows things down.
Working with crypto wallet developers that have already dealt with these systems changes the pace. A lot of decisions don’t need to be rediscovered—custody model, key handling, how to structure integrations. That shortens the early stages and avoids some predictable mistakes.
Security is one of the main reasons teams don’t build wallets entirely in-house. It’s not just about encryption, but about how the whole system is arranged—where keys live, how signing is isolated, how access is controlled. Getting that wrong is expensive to fix later.
The same goes for blockchain integrations. Each network behaves differently, and supporting several at once quickly turns into a coordination problem. Teams with prior experience usually already have patterns for handling that, instead of building everything from zero.
There’s also a practical aspect. Wallets are rarely standalone products—they’re part of something larger: a trading platform, a payment system, a SaaS product. Here the experience with SaaS platforms starts to matter, because the wallet has to fit into a system that keeps evolving, not just run on its own.
Final Thoughts
Wallets don’t come together in one step. It starts with a rough idea, then a set of constraints—custody, networks, how keys are handled. After that, everything turns into implementation details: integrations, signing flows, edge cases. The launch is just where those decisions get tested under real conditions.
Most of the trade-offs sit in the same place. Make it safer—you add friction. Make it simpler—you risk hiding something important. Add more chains—complexity grows. There’s no clean balance, just choices that have to hold up over time.
What matters is whether the system survives real use. Not just normal flows, but delays, failed transactions, user mistakes, network issues. That’s where wallets tend to break if something was overlooked early.
That’s also why teams don’t usually treat wallets as isolated features. They’re tied to the rest of the product—trading, payments, whatever sits around them. If that part isn’t thought through, the wallet won’t hold on its own.
If you’re building one, it’s worth working with those who’ve already dealt with these trade-offs in practice. Shakuro has been working in Web3 and fintech long enough to know where things usually break—and how to avoid that early on.
