For those who prefer to listen rather than read, this article is also available as a podcast on Spotify.
Contents:
“So, how are you handling data encryption?” This question keeps you up at night, especially if you are a founder or a CTO. When you’re in fintech moving money, healthcare dealing with sensitive patient records, or e-commerce holding credit card details, the stakes are incredibly high. One small slip-up, one tiny vulnerability you didn’t catch, and suddenly you’re staring down a PR nightmare, hefty fines, and users who won’t come back.
Many founders think their app is “secure enough” because they use a popular framework. But it’s not a strategy. Protecting your users is a must, and in regulated industries like banking or health, you really don’t have a choice.
If you’re ready to stop guessing and start implementing mobile app security that doesn’t kill your velocity, stick around. I’m going to break down exactly how to lock things down without losing your mind.
Why Mobile App Security Is Critical for Your Business
Protecting User Data = Protecting Your Brand
We live in a time where news about data breaches hits our feeds almost daily. But when you’re running a business, especially one handling money or health info, you can’t afford to ignore the hum. The threats are getting sharper, more automated, and they don’t take holidays.
Think about what actually happens when things go wrong. Sure, there are fines. Those hurt. But the real punch to the gut is the look on your users’ faces when they realize you couldn’t keep their secrets safe. Recovering from a shattered reputation is like trying to un-ring a bell. You just can’t do it.
People hand over their most sensitive stuff to your app because they believe you’ll guard it. It’s a quiet promise. When that promise breaks, the backlash is immediate and brutal. Social media lights up, reviews tank, metrics go down, and suddenly, that cool feature you launched last week doesn’t matter anymore. Nobody cares how smooth your UI is if their credit card number is floating around on the dark web.
That sticks with you. It changes how you approach everything. So, when we talk about mobile app data protection, we are talking about the very soul of your business. If you protect your users’ data, you’re protecting the only thing that really keeps the lights on: their faith in you.

Mobile App for Construction Lead Generation Platform by Shakuro
Common Security Vulnerabilities in Mobile Apps
Insecure Data Storage
Assuming that the data is in a safe little bubble since it’s sitting locally on a user’s phone is an unwise idea. Phones get lost, stolen, or even just borrowed by a “friend” for a minute.
If your app is caching sensitive info, like API keys, user tokens, or maybe even full credit card numbers, in plain text within the local database or shared preferences, you’re basically leaving the front door wide open. Anyone with basic tools can pull that file off the device and hijack the account instantly. It is just lazy storage.
Honestly, it’s an easy fix, but if you don’t think about it during the build phase, it slips through. You end up with a situation where a thief just needs physical access to the phone. That’s a nightmare scenario you really want to avoid.
Insufficient Authentication and Authorization
We’ve all used apps where the login feels flimsy, right? Maybe it accepts a four-digit PIN as a “strong” password, or worse, it lets you stay logged in forever without checking if it’s still really you. It’s insufficient authentication, and it’s a goldmine for attackers. If your session management is weak, someone can grab a session ID and pretend to be your user indefinitely. It’s scary how common this is.
Data protection in mobile apps depends on authorization as well. I’ve seen cases where a regular user could just tweak a number in the API request and suddenly access an admin panel or view someone else’s medical records. It happens because the backend trusts the request without double-checking permissions. You agree that sounds like a basic oversight, but under pressure to ship, these checks often get rushed or skipped. The result is users getting into places they absolutely shouldn’t be, and you having no idea until it’s too late.
Lack of Encryption
Sometimes I feel like people treat mobile app encryption as this optional extra. “Nice to have if we have a budget.” No, no, no. Without it, everything flying between the app and your server is basically sent via postcard. Anyone sniffing the network (and public Wi-Fi makes this trivial) can read it all.
You need encryption at rest, too. If a hacker manages to dump your database, encrypted data looks like gibberish to them. Unencrypted one is an open book.
Founders say, “Well, our users are behind a firewall,” or “We use HTTPS, so we’re good.” But HTTPS only covers the transit part. What about when that data sits on the device or in your backup logs? If it’s not scrambled both ways, you’re taking a massive gamble. And in industries like healthcare or finance, that gamble is often illegal. You really don’t want to explain to a regulator why you thought encryption was optional.

Prime Chat AI Mobile Assistant by Shakuro
Best Practices for Securing Mobile Apps
Implement Strong User Authentication
Many people just use “Password123” or reuse the same one for their banking app and their pizza delivery account. So you need layers. That’s where Multi-Factor Authentication (MFA) comes in. I know, I know, nobody loves typing in a code from their text messages, but it stops so many attacks cold. It’s that extra step that makes a hacker’s life miserable.
Biometrics are a game-changer here as well. Face ID and fingerprints are serious security tools that users actually like because they’re fast. Teams that roll out biometric logins as a part of app security best practices see way fewer support tickets about forgotten passwords, too.
But don’t forget the session part. Just because someone logged in once doesn’t mean they should stay logged in forever. Make sure your sessions time out after a while, especially if the app is idle. It’s a little annoying for the user to log in again, sure, but it’s way better than someone picking up their unlocked phone and draining their bank account.
Encrypt Sensitive Data
Let’s circle back to encryption because it really is the backbone of everything. You need to always encrypt everything. This applies to the data sitting quietly in a database (at rest) or zooming across the internet to your server (in transit). Think of it like putting your valuables in a safe before moving them across town. Even if the truck gets hijacked, the thieves can’t open the safe.
For data in transit, TLS (that’s the successor to SSL) is non-negotiable. Don’t try to cut corners with older versions either, and stick to the latest standards instead. For data at rest, use strong algorithms like AES-256. It sounds technical, but most modern frameworks make this pretty straightforward to implement.
The key to solid mobile app encryption is consistency. Don’t just encrypt the credit card numbers and leave the user’s address book in plain text. Attackers are clever: they’ll go for the low-hanging fruit. If you scramble it all, you force them to give up. It’s a bit of work upfront, but totally worth it.
Secure the Backend and APIs
Your mobile app is just the front door. The real house is your backend. You can build the most secure app in the world, but if your API endpoints are wide open, you’re still in trouble. Teams spend months hardening their iOS and Android clients, only to get breached because an API didn’t check who was asking for data. It’s like having a steel door but leaving the windows unlocked.
Your backend needs to treat every single request as suspicious. Never trust the client. Validate everything coming in, limit how often someone can hit an endpoint (rate limiting is your friend here), and make sure your authorization logic is tight.
Also, keep an eye on those API keys. Don’t hardcode them in the app because that’s basically handing them out to anyone who knows how to decompile an APK. Use a secure gateway or a management tool to keep things locked down. Honestly, securing the backend feels less glamorous than tweaking the app UI, but it’s where the real battle is fought.
Secure Mobile Code
Finally, let’s talk about the code itself. It’s easy to get so focused on features that you forget about how the code is written. But sloppy coding practices are an invitation for injection attacks, where hackers slip malicious code into your app to do their bidding.
Following app security best practices is for everyone. Things like input validation (checking that the data a user types is actually what you expect) can stop a huge chunk of attacks before they even start.
One of these practices is obfuscating your code. It’s not a silver bullet, but it makes it much harder for attackers to reverse-engineer your app and find weaknesses. Doing regular code reviews with a security mindset helps catch these issues early. Maybe bring in a second pair of eyes who wasn’t involved in writing that specific module. Fresh eyes spot things you miss because you’ve been staring at the same logic for weeks. It takes a bit more time in the development cycle, but it saves you from a massive headache later.
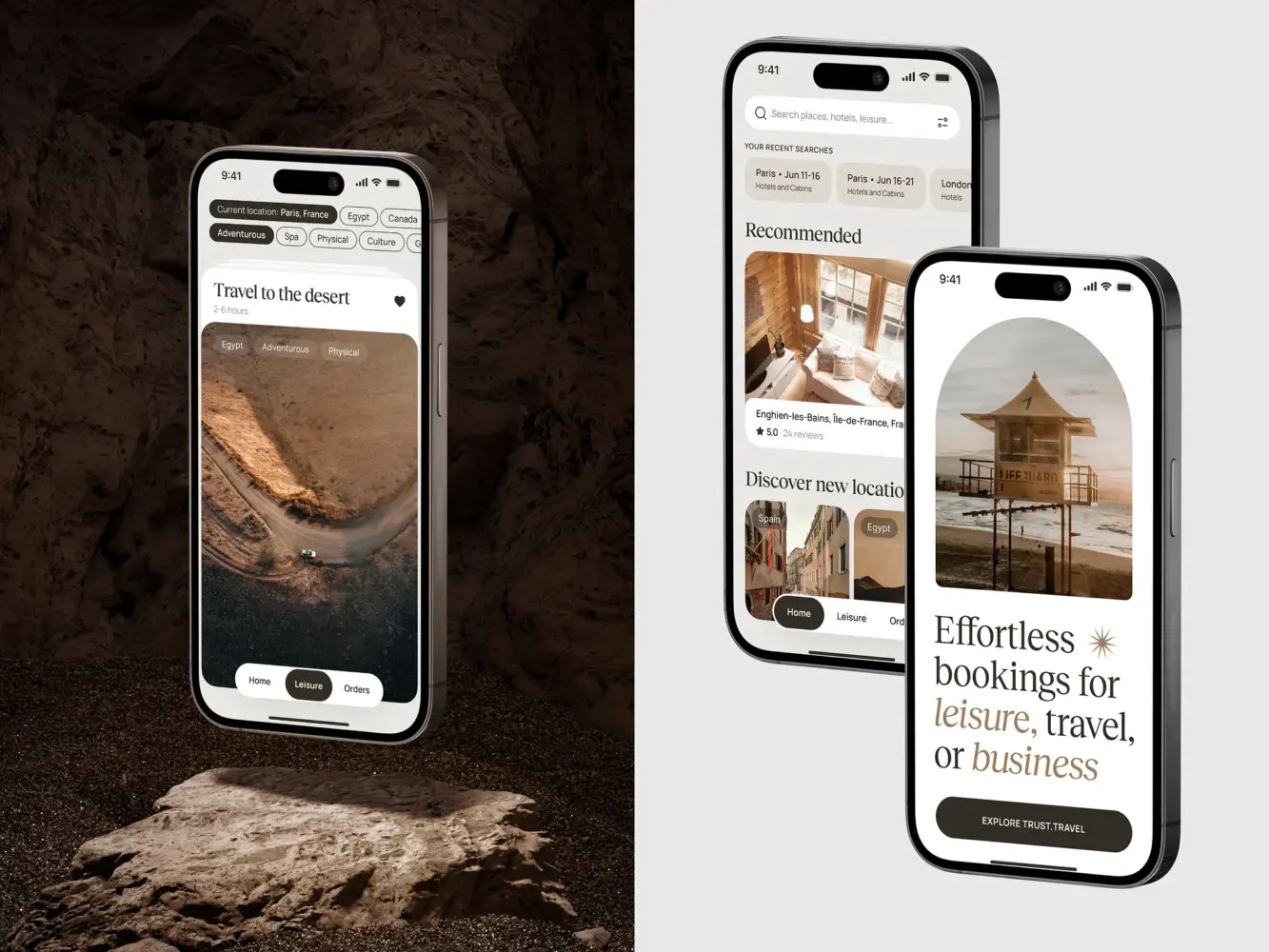
Travel Booking Mobile App Design by Shakuro
How to Stay Compliant with Industry Regulations
Data Protection Regulations (GDPR, HIPAA, etc.)
If you’re in fintech or healthcare, you already know the alphabet soup of regulations can feel overwhelming. GDPR, HIPAA, CCPA, and many others. But don’t think of these rules as just bureaucratic red tape designed to slow you down.
They’re actually a pretty solid blueprint for building a secure product. When GDPR says you need to minimize data collection, it’s basically telling you, “Hey, don’t hoard data you don’t need, because if you don’t have it, you can’t lose it.” Simple logic, right?
HIPAA is even stricter, especially for anything touching patient health info. It explains who can see what, when, and why.
These regulations force you to look at the whole picture, not just the shiny parts. They shape your mobile app security requirements by making you accountable for every byte of data. Once you align your app with these standards, you’re building a product that respects user privacy by default. That’s a huge selling point these days.
The Role of Security Audits in Compliance
It sounds expensive, time-consuming, and kinda scary. Who wants strangers poking around their code? But you can’t prove you’re compliant just by saying so. You need evidence. Regular security audits, whether internal or by a third party, are that evidence. They’re like a health checkup for your app. You might feel fine, but wouldn’t you rather catch that small issue before it becomes a heart attack?
Audits dig into the stuff you might miss because you’re too close to the project. They check your encryption keys, test your authentication flows, and see if your data retention policies actually match what you told regulators you’d do. Teams that skip audits to save money get hit with a massive fine later because they couldn’t prove they were following the rules during an investigation. The cost of the audit would’ve been a drop in the bucket compared to the penalty.
Plus, having that stamp of approval from a reputable auditor builds trust with partners and investors instantly. It shows you’re serious. So yeah, schedule those audits and make them routine. It’s a little painful sometimes, but it keeps you out of hot water and proves you’re playing by the rules.
The Impact of App Security on User Trust and Engagement
How Security Features Build User Trust
You know, we often talk about “trust signals” in marketing, like customer testimonials or shiny badges on a landing page. But in the mobile world, the real trust signal is invisible. It’s the feeling a user gets when they open your app and nothing weird happens. No suspicious pop-ups, no weird lag while logging in, just a smooth, secure experience. When you implement visible data protection in mobile apps, like a clean biometric login or a clear notification when a new device accesses their account, you’re silently telling them, “We’ve got your back.”
When product teams highlight these security measures as a feature, users actually respond positively. It’s like seeing a bank with heavy vault doors, which makes you feel like your money is safe. In fintech especially, I’ve seen conversion rates jump just because the onboarding flow clearly explained how data was protected.
Users are savvy now. They know the risks. If your app feels flimsy, they’ll hesitate to connect their bank account or upload health records. But if you make mobile app security part of the user experience, it becomes a reason to stay. You create an environment where users feel comfortable enough to engage deeply.
Reducing Churn with Robust Security
Nothing kills an app faster than a breach. You can have the best features, the slickest design, and the coolest community, but if users feel unsafe, they’re gone. And they don’t just leave quietly; they leave negative reviews.
High churn rates after a security incident are a relationship breakdown. Once a user feels betrayed, getting them back is nearly impossible. Apps can lose 30% of their active user base in a single week after a minor leak. The recovery can take years, and some people will never come back.
Think about it from their perspective. If your app leaks their data, you’ve basically broken a promise. It’s personal. They entrusted you with something valuable, and you dropped the ball. The emotional fallout is huge. They feel violated, angry, and honestly, a bit foolish for trusting you in the first place. That’s a heavy emotion to overcome.
On the flip side, secure mobile app development acts as a retention engine. When users know their data is locked down tight, they stick around. They’re more likely to upgrade to premium plans, share the app with friends, and forgive the occasional bug.
Security is an investment in loyalty. You agree, keeping a user is way cheaper than trying to win back a thousand angry ones, right? So, treating security as a core part of your retention strategy is essential for survival.
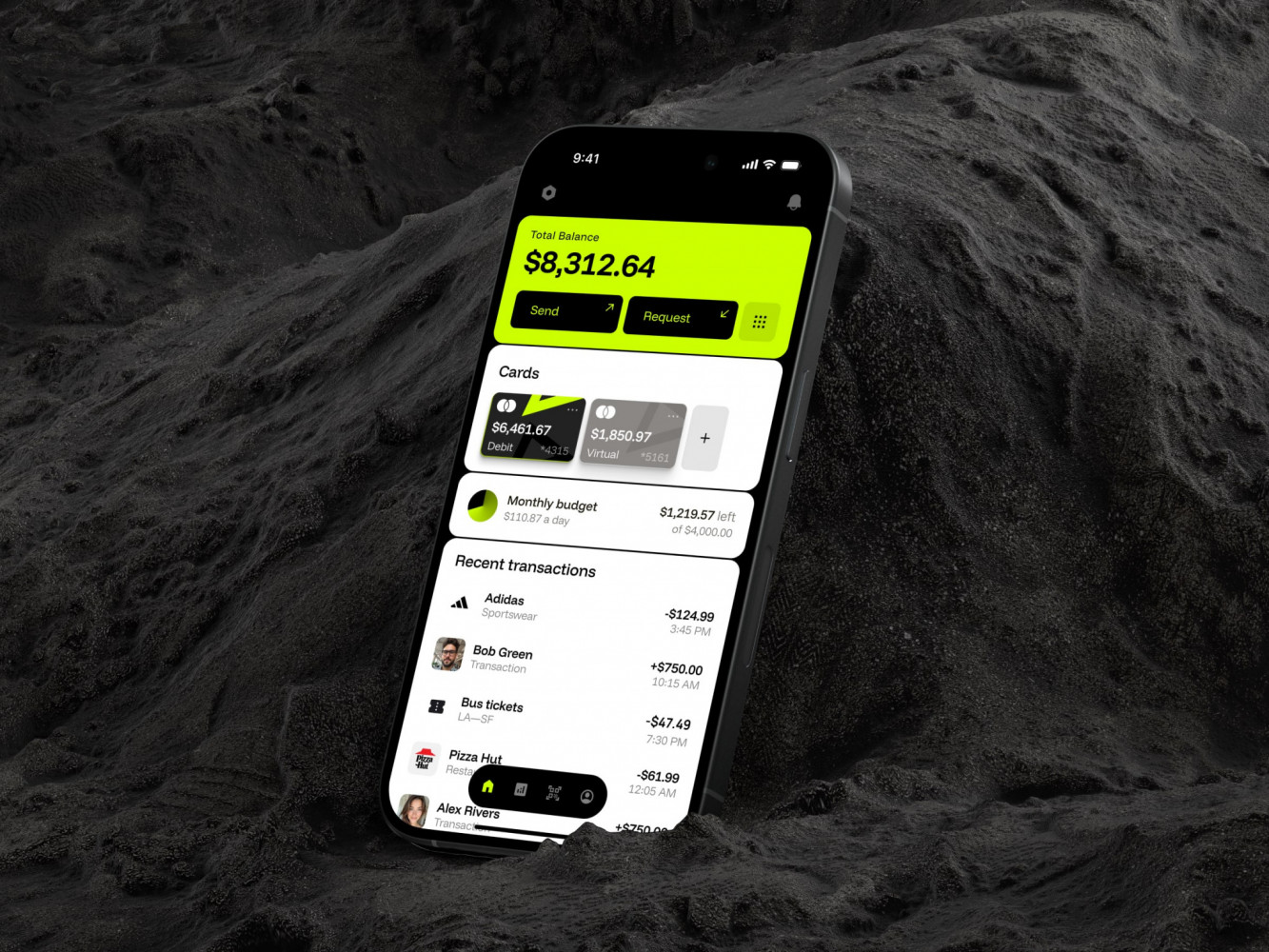
Mobile Banking App by Conceptzilla
Mobile App Security Testing: Tools and Techniques
Penetration Testing for Mobile Apps
You’ve built the walls and installed the locks. But how do you really know they hold up? That’s where penetration testing comes in.
It’s ethical hacking, plain and simple. You get experts, either an internal red team or external consultants, to attack your app exactly like a real criminal would. Instead of running a script, they get creative. They’ll try to intercept traffic on a sketchy coffee shop Wi-Fi, tamper with the app binary, or trick your server into giving up data it shouldn’t.
It might be embarrassing for the team, sure, but it’s way better than finding mobile app security vulnerabilities out after a real breach. The beauty of pen testing is that it finds the logic flaws and weird edge cases that automated scanners miss. It gives you a reality check.
Sure, it can be a bit stressful having someone poke holes in your hard work, but honestly, it’s the only way to sleep well knowing you’ve faced the worst-case scenario before the bad guys do.
Automated Security Testing Tools
Now, you can’t hire hackers to test your app every time a developer pushes a new line of code. That’d be crazy expensive and slow everything down. In these cases, you can use automated tools.
They’re like having a security guard who never sleeps, constantly scanning your perimeter for open windows. Tools like OWASP ZAP and Burp Suite are industry standards for a reason. They sit between your app and the server, intercepting traffic and fuzzing inputs to see if anything breaks. They’re great at catching the low-hanging fruit: things like missing headers, weak encryption protocols, or basic injection flaws.
There are tools like Saucelabs or similar that help you see how the app behaves in real-time on actual devices. You can spot if sensitive data is accidentally leaking into logs or screenshots. Integrating these into your CI/CD pipeline is a game-changer.
It feels a bit like having a safety net while walking a tightrope. Of course, these tools aren’t magic. They’ll give you false positives sometimes, which can be annoying. You still need a human to interpret the results. But when used right, they really help catch mobile app security vulnerabilities early, freeing up your team to focus on the complex stuff.

AI Chef Mobile App by Shakuro
How Shakuro Ensures the Security of Your Mobile App
Shakuro’s Security-First Development Process
When creating apps, we pay close attention to the data safety. The process starts with signing an NDA and creating roadmaps, where our managers help you decide what parts of the projects should be extra protected. We check the industry and market official regulations, making sure that the app stays compliant.
During development, the team implements the best industry practices, like secure code with review, data encryption, 2FA & MFA authentication, biometrics, etc. Using well-known tools, we build robust backend infrastructure closely connected with the frontend.
When cookie-cutter solutions are not enough, we build custom instruments. They allow us to speed up secure mobile app development, delivering responsive, high-performance solutions faster.
Successful Security-Centric Mobile Apps Delivered by Shakuro
Our approach is supported by dozens of real-life cases from the portfolio.
Zad is a Shariah-compliant mobile investment app. They needed a necessary level of security because of storing sensitive info and fintech industry regulations (GDPR, KYC). At the same time, the target audience included beginners, that’s why we avoided elaborate workflows, for example, for 2FA or Face ID. At the same time, the team built a reliable backend with robust databases (PostgreSQL, MongoDB) to help protect user data. So people can easily manage their financial assets without worrying about exposing their information.
For Bless You, a healthcare platform from the Kingdom of Saudi Arabia, we implemented strict mobile app security measures as well. Aimed at both residents and tourists, it had to comply with the country’s regulations about healthcare and culture. Not to mention complying with international standards like HIPAA. We created a robust infrastructure that was able to store large amounts of healthcare data and support pro-level features, such as telemedicine.
Using Swift and React, our developers built a reliable architecture for Select, a private membership community. The mobile app had to deal with users’ personal data, for example, reservations, service chats, etc. We implemented best industry practices during cross-platform development, such as secure coding, data encryption, and secure APIs.
So yeah, if you want to integrate solid security measures into your app, reach out to us. Together, we will create a comprehensive strategy to build a high-performance and secure application.
